Best Practices for Modern Software Development

In today's rapidly changing software landscape, it is more important than ever to use best practices to develop high-quality software that meets the needs of users. This book provides a comprehensive overview of the best practices for modern software development, covering topics such as agile development, DevOps, cloud computing, and security.
5 out of 5
| Language | : | English |
| File size | : | 105901 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 528 pages |
Agile Development
Agile development is a software development methodology that emphasizes iterative development, team collaboration, and customer feedback. It is based on the idea that software development is a complex and unpredictable process, and that it is better to embrace this complexity and adapt to change rather than to try to predict and control it.
There are many different agile development methodologies, but they all share some common principles, such as:
- Iterative development: Agile development projects are typically broken down into small, iterative cycles. This allows teams to get feedback from customers early and often, and to make changes to the software as needed.
- Team collaboration: Agile development teams are typically cross-functional, meaning that they include members with different skills and expertise. This allows teams to work together to solve problems and deliver high-quality software.
- Customer feedback: Agile development teams involve customers in the development process. This allows teams to get feedback on the software early and often, and to make changes to the software as needed.
DevOps
DevOps is a software development practice that emphasizes collaboration between development and operations teams. It is based on the idea that these two teams should work together to deliver high-quality software that meets the needs of users.
DevOps practices can include:
- Continuous integration: This practice involves automating the process of integrating new code changes into the main codebase. This helps to ensure that the codebase is always up-to-date and stable.
- Continuous delivery: This practice involves automating the process of deploying new code changes to production. This helps to ensure that new features and bug fixes are delivered to users quickly and reliably.
- Infrastructure as code: This practice involves managing infrastructure using code. This helps to ensure that infrastructure is provisioned and managed in a consistent and repeatable way.
Cloud Computing
Cloud computing is a model for delivering computing services over the internet. It allows businesses to access computing resources, such as servers, storage, and databases, without having to own and maintain them. Cloud computing can provide many benefits, such as:
- Scalability: Cloud computing allows businesses to scale their computing resources up or down as needed. This can help businesses to meet changing demand without having to over-provision or under-provision resources.
- Cost savings: Cloud computing can be more cost-effective than traditional on-premises computing. This is because businesses only pay for the resources they use, and they do not have to invest in and maintain their own hardware.
- Reliability: Cloud computing providers offer high levels of reliability. This is because they have multiple data centers located around the world, and they can quickly failover to a backup data center in the event of an outage.
Security
Security is a critical aspect of software development. It is important to consider security throughout the software development lifecycle, from design to deployment. Some of the key security best practices include:
- Use secure coding practices: Secure coding practices can help to prevent vulnerabilities from being introduced into software. These practices include using strong passwords, validating input data, and escaping special characters.
- Implement security controls: Security controls can help to protect software from unauthorized access, data breaches, and other security threats. These controls include firewalls, intrusion detection systems, and access control lists.
- Monitor for security threats: It is important to monitor for security threats and to respond to them quickly. This can be done by using security monitoring tools and by staying up-to-date on the latest security threats.
The best practices for modern software development are constantly evolving. However, the principles of agile development, DevOps, cloud computing, and security remain the same. By following these best practices, you can develop high-quality software that meets the needs of users and helps your business succeed.
5 out of 5
| Language | : | English |
| File size | : | 105901 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 528 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Viet Thanh Nguyen
Viet Thanh Nguyen Molly Stanton
Molly Stanton Natasha Lindstaedt
Natasha Lindstaedt Michael Rinaldini
Michael Rinaldini Thomas Gold
Thomas Gold Nicholas J Wade
Nicholas J Wade Mindy Tsai
Mindy Tsai Naielah Ackbarali
Naielah Ackbarali Nicole Crystals
Nicole Crystals Nicole Osmanski
Nicole Osmanski Os Guinness
Os Guinness Mirav Tarkka
Mirav Tarkka Nick Fancher
Nick Fancher William Lawlor
William Lawlor Scott Dixon
Scott Dixon Nick Vulich
Nick Vulich Morgan Sinclair
Morgan Sinclair Michael Zhuang
Michael Zhuang Sholem Asch
Sholem Asch Michael Shapiro
Michael Shapiro
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Walter SimmonsNever Box With a Kangaroo 11: Magic Bone - The Key to Unlocking Your Inner...
Walter SimmonsNever Box With a Kangaroo 11: Magic Bone - The Key to Unlocking Your Inner... Harvey HughesFollow ·15k
Harvey HughesFollow ·15k Dwight BellFollow ·10.7k
Dwight BellFollow ·10.7k Bruce SnyderFollow ·3.9k
Bruce SnyderFollow ·3.9k Barry BryantFollow ·3k
Barry BryantFollow ·3k Julio Ramón RibeyroFollow ·16.3k
Julio Ramón RibeyroFollow ·16.3k Craig CarterFollow ·4.3k
Craig CarterFollow ·4.3k Darnell MitchellFollow ·18.1k
Darnell MitchellFollow ·18.1k Charlie ScottFollow ·10.4k
Charlie ScottFollow ·10.4k
 Samuel Beckett
Samuel BeckettPortrait of the Plague Doctor: A Chilling Tale of Fear...
Prologue: A...
 Elliott Carter
Elliott CarterTrends in Modeling and Simulation Studies in...
Unveiling the Convergence of...
 Natsume Sōseki
Natsume SōsekiCells For Kids: Science For Children
Unlock the Microscopic...
 Anthony Wells
Anthony WellsUnlock the Power of Understanding: Embrace the African...
Embark on a Journey of Truth,...
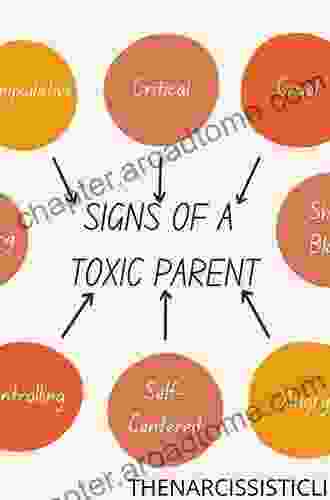
 Forrest Reed
Forrest ReedBreaking Free: Healing from Toxic Relationships Between...
Are you struggling...
5 out of 5
| Language | : | English |
| File size | : | 105901 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 528 pages |